
Information broke right this moment of a “mom of all breaches,” sparking extensive media protection full of warnings and fear-mongering. Nonetheless, it seems to be a compilation of beforehand leaked credentials stolen by infostealers, uncovered in knowledge breaches, and by way of credential stuffing assaults.
To be clear, this isn’t a brand new knowledge breach, or a breach in any respect, and the web sites concerned weren’t not too long ago compromised to steal these credentials.
As an alternative, these stolen credentials have been seemingly circulating for a while, if not for years. It was then collected by a cybersecurity agency, researchers, or menace actors and repackaged right into a database that was uncovered on the Web.
Cybernews, which found the briefly uncovered compilation, said it was saved in a format generally related to infostealer malware, although they didn’t share samples
An infostealer is malware that makes an attempt to steal credentials, cryptocurrency wallets, and different knowledge from an contaminated system. Through the years, infostealers have grow to be a large drawback, resulting in breaches worldwide.
A majority of these malware impression each Home windows and Macs, and when executed, will collect all of the credentials it will probably discover saved on a tool and save them in what known as a “log.”
An infostealer log is usually an archive containing quite a few textual content recordsdata and different stolen knowledge. The textual content recordsdata comprise lists of credentials stolen from browsers, recordsdata, and different purposes.
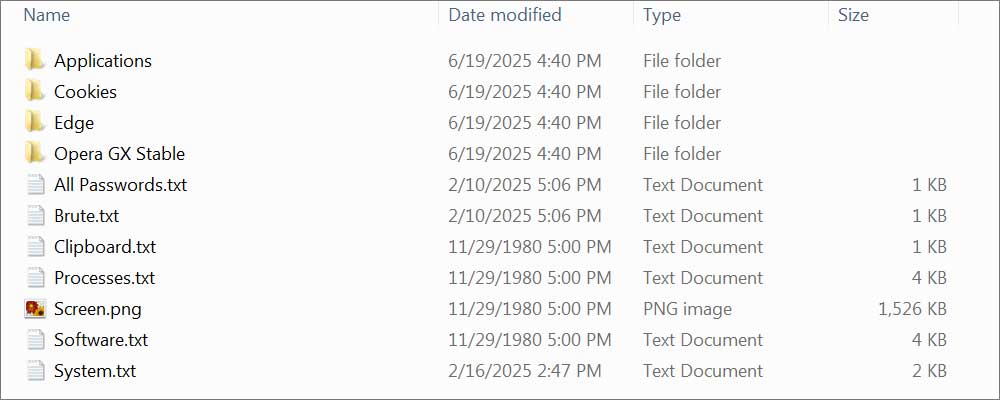
Supply: BleepingComputer
Stolen credentials are normally saved one per line within the following format:
URL:username:password
Generally, the delimiter between every element is modified to a comma, semicolon, or sprint.
For instance, the next is how an infostealer will save credentials stolen from a tool to a log:
https://www.fb.com/:jsmith@instance.com:Databr3achFUd!
https://www.financial institution.com/login.php:jsmith:SkyIsFa11ing#
https://x.com/i/move/login:jsmith@instance.com:StayCalmCarryOn
If somebody is contaminated with an infostealer and has a thousand credentials saved of their browser, the infostealer will steal all of them and retailer them within the log. These logs are then uploaded to the menace actor, the place the credentials can be utilized for additional assaults or offered on cybercrime marketplaces.
The infostealer drawback has gotten so dangerous and pervasive that compromised credentials have grow to be one of the widespread methods for menace actors to breach networks.
We have now a webinar subsequent month titled “Stolen credentials: The New Entrance Door to Your Community” that focuses on infostealers, compromised credentials, and the way organizations can defend themselves.
This drawback has additionally led regulation enforcement worldwide to actively crack down on these cybercrime operations in latest actions, akin to “Operation Safe” and the disruption of LummaStealer.
As infostealers have grow to be so plentiful and generally used, menace actors launch large compilations totally free on Telegram, Pastebin, and Discord to achieve status among the many cybercrime neighborhood or as teasers to paid choices.
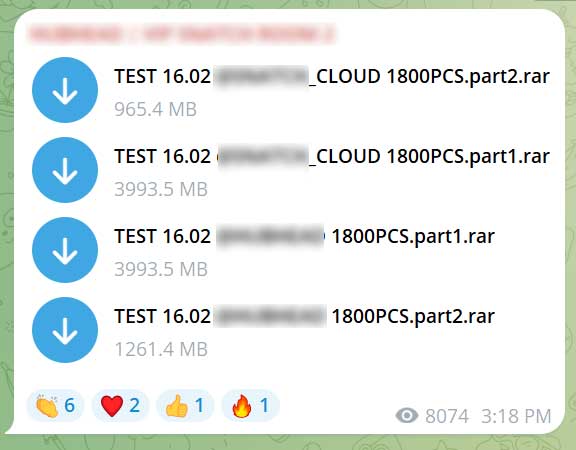
Supply: BleepingComputer
To see what number of passwords are given away totally free, the only 1,261.4 MB file within the picture above contained over 64,000 credential pairs.
There are hundreds, if not a whole bunch of hundreds, of equally leaked archives being shared on-line, leading to billions of credentials data launched totally free.
Many of those free archives have been seemingly compiled into the huge database that was briefly uncovered and seen by Cybernews.
Related credential collections have been launched prior to now, such because the RockYou2024 leak, with over 9 billion data, and “Colection #1,” which contained over 22 million distinctive passwords.
Regardless of the excitement, there is no proof this compilation comprises new or beforehand unseen knowledge
What must you do?
So, now that there was a large leak of credentials seemingly stolen via infostealers, knowledge breaches, and credential-stuffing assaults, chances are you’ll be questioning what it’s best to do.
Crucial step is to undertake and keep good cybersecurity habits it’s best to already be following.
Should you’re involved that an infostealer may be current in your laptop, scan your system with a trusted antivirus program earlier than altering any passwords. In any other case, newly entered credentials could possibly be stolen as properly.
When you’re assured your system is clear, deal with enhancing your password hygiene.
Meaning utilizing a novel, sturdy password for each website you utilize, and counting on a password supervisor to maintain them organized and safe.
Nonetheless, even distinctive passwords will not show you how to keep protected in case you are hacked, fall for a phishing assault, or set up malware.
Due to this fact, it’s essential that you just additionally use two-factor authentication (2FA) together with an authentication app, like Microsoft Authenticator, Google Authenticator, or Authy, to handle your 2FA codes. Some password managers, like Bitwarden and 1Password, additionally embrace authentication performance, permitting you to make use of one utility for each.
With 2FA enabled, even when a password at a website is compromised, menace actors can not entry the account with out your 2FA code.
As a normal rule, it’s best to keep away from utilizing SMS texts to obtain 2FA codes, as menace actors can conduct SIM-swapping assaults to hijack your cellphone quantity and acquire them.
As for this leak, with this many credentials leaked, there’s a likelihood one of many readers of this text shall be listed within the compilation.
Nonetheless, do not panic and stress about it, working round altering all of your passwords. As an alternative, take this chance to enhance your cybersecurity habits.
To verify in case your credentials have appeared in recognized breaches, think about using companies like Have I Been Pwned.
And should you use the identical password throughout a number of websites, now could be the time to modify to distinctive ones.
That approach, leaks like this grow to be far much less harmful to you.

Patching used to imply complicated scripts, lengthy hours, and infinite hearth drills. Not anymore.
On this new information, Tines breaks down how fashionable IT orgs are leveling up with automation. Patch sooner, scale back overhead, and deal with strategic work — no complicated scripts required.

